Rate Limiting
System Design Mastery
Introduction to System Design
Fundamentals, why it matters, key conceptsScalability Fundamentals
Horizontal vs vertical scaling, stateless designLoad Balancing & Caching
Algorithms, Redis, CDN patternsDatabase Design & Sharding
SQL vs NoSQL, replication, partitioningMicroservices Architecture
Decomposition, discovery, testing, resilienceAPI Design & REST/GraphQL
RESTful principles, GraphQL, gRPCMessage Queues & Event-Driven
Kafka, outbox, event sourcing, idempotent consumersCAP Theorem & Consistency
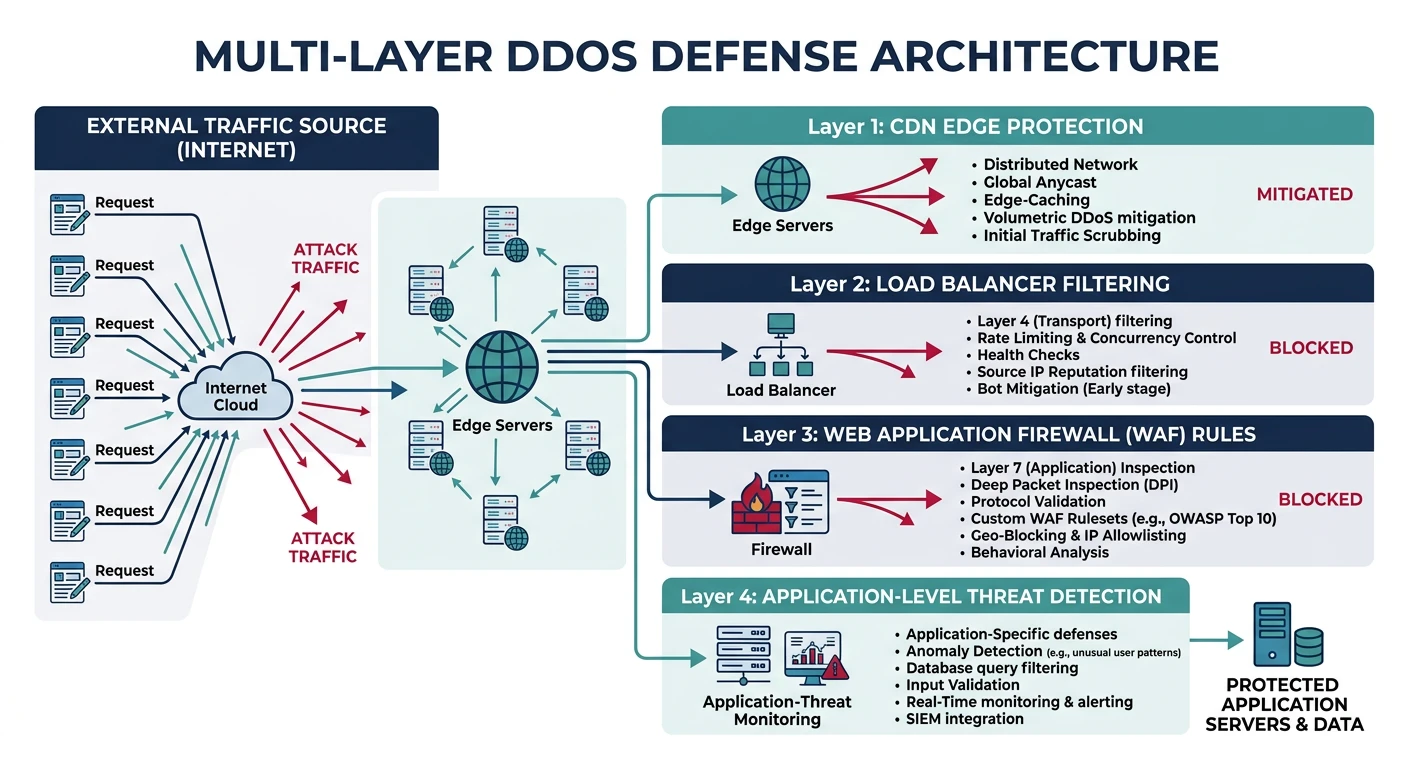
Distributed trade-offs, eventual consistencyRate Limiting & Security
Throttling algorithms, DDoS protectionMonitoring & Observability
Logging, metrics, distributed tracingReal-World Case Studies
URL shortener, chat, feed, video streamingData Modeling & Schema Design
Data modeling, schema design, indexingDistributed Systems Deep Dive
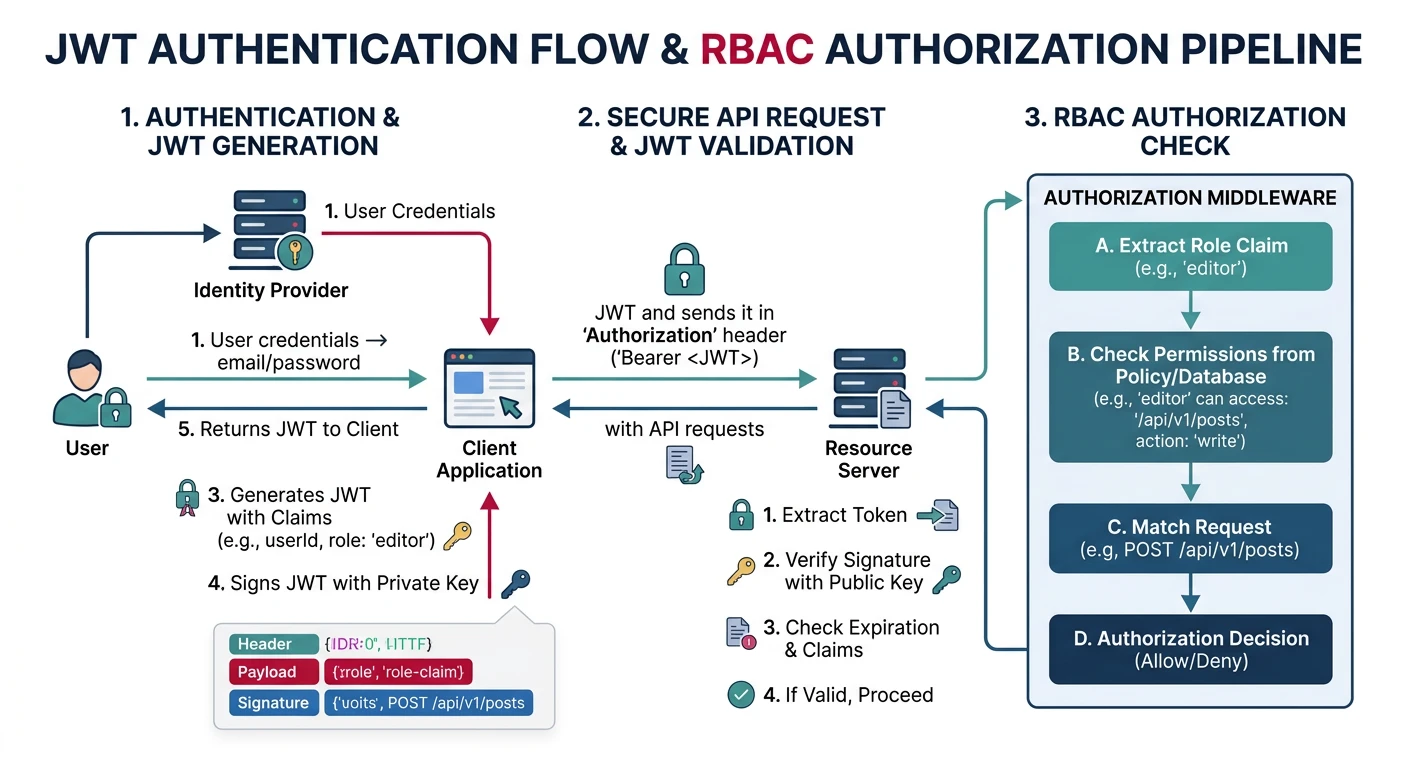
Consensus, Paxos, Raft, coordinationAuthentication & Security
OAuth, JWT, zero trust, complianceQuestions & Trade-offs
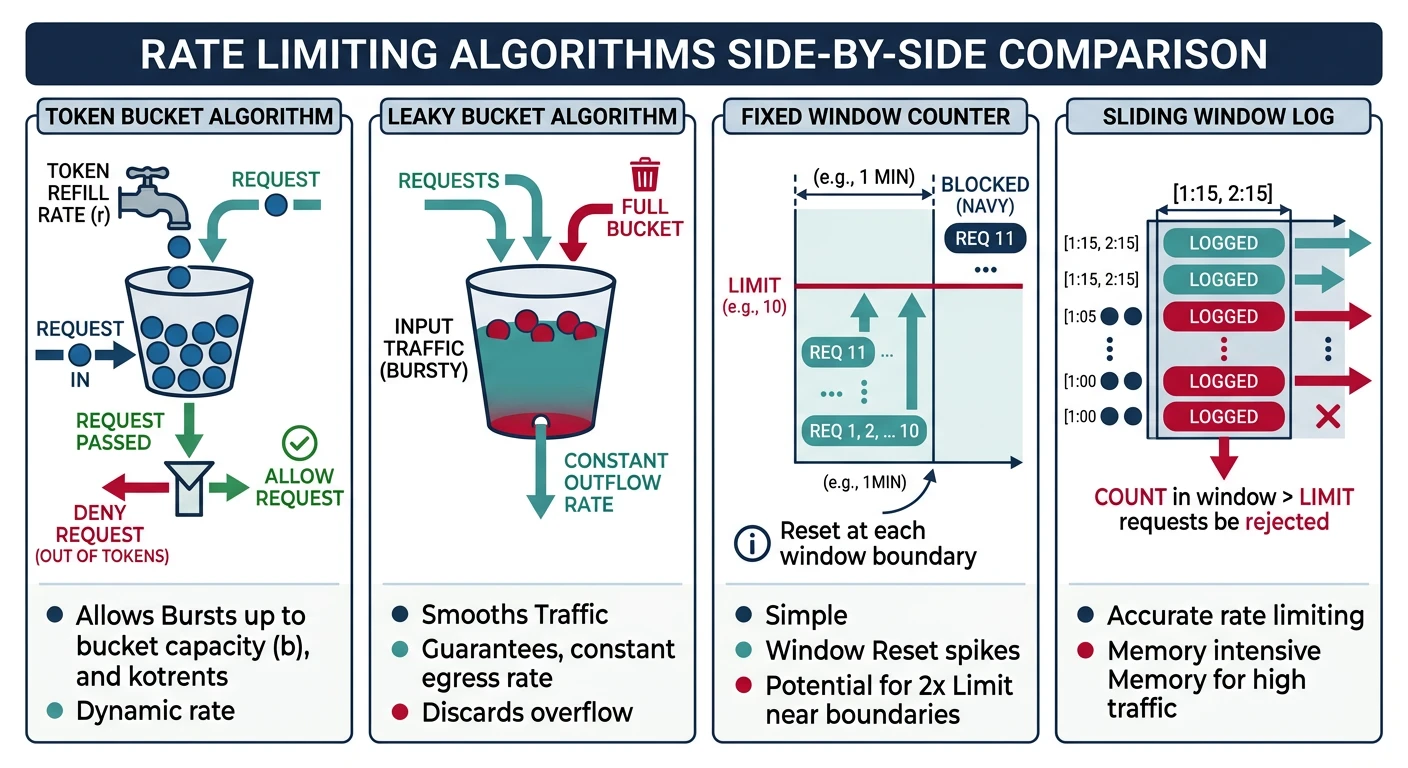
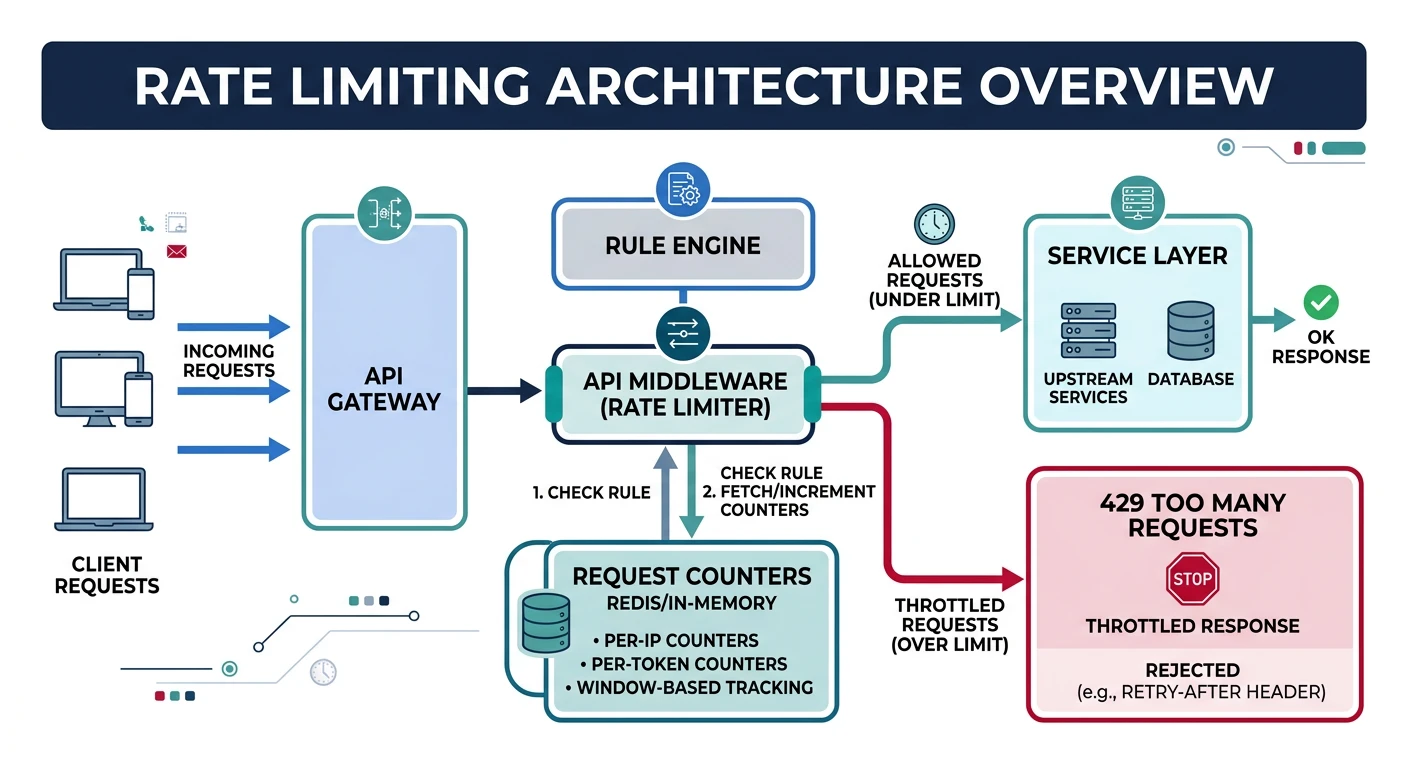
Common questions, SQL vs NoSQL, push vs pullRate limiting controls the number of requests a client can make to your API within a given time window. It protects your services from abuse, ensures fair usage, and maintains system stability under load.
Why Rate Limit?
- Prevent abuse: Stop malicious actors from overwhelming your system
- Ensure fairness: Give all users equal access to resources
- Control costs: Limit expensive operations and API calls
- Protect downstream: Prevent cascading failures to dependent services
- Maintain SLAs: Guarantee performance for paying customers